Introducing the Volerion Vulnerability Intelligence Platform
-
 Ruben Bos
Ruben Bos - 13 Apr, 2026
There is a reason why most CVE dashboards do not make it as a daily driver.
At first, it looks good. You ingest the feed, sort by score, add a few alerts, and ship. Then volume rises, errors accumulate, and your analysts spend their time manually validating (non-)matches instead of making decisions.
The problem is rarely the UI, but the data that powers it.
Today, we are introducing the Volerion Vulnerability Intelligence Platform beta, a practical system for turning vulnerability data into defensible decisions at scale.
Why This Matters Now
The security market has no shortage of visualization software. What it lacks is data you can automate against without constantly second-guessing it.
This problem increases in size and complexity because the number of CVEs published each year keeps rising, and the trend is not flattening. In the Vulnerability Forecast 2026, FIRST projected that we could hit 100,000 published CVEs in 2026.
Any intelligence platform is only useful as useful as the data underneath. Most teams run into the same issues, including coverage gaps that create blind spots, inconsistent field semantics between records, and low-confidence enrichment that cannot be audited.
When those problems exist, every downstream workflow becomes fragile. A filter that worked yesterday breaks tomorrow. A severity threshold floods you with noise. A routing rule misses the one item that actually mattered. Traditional dashboards break down in exactly this way, especially when public data arrives with gaps, inconsistencies, or delays that force analysts to keep re-checking views and second-guessing what they are seeing.
This is why we invested years in the foundation before building the workflow layer to deliver complete coverage, accurate enrichment, and deterministic analysis. If the substrate is unstable, every shiny dashboard on top of it is unstable too.
The Foundation
Volerion is inherently an API-first, data-driven company. This puts us in the unique position of utilizing our own quality enrichment data for whatever we build around it.
Instead of treating CVEs as a standalone blob of unstructed data with a score attached, we normalize and enrich each record into structured, queryable entities that can be reasoned over consistently.
That means standardized CVE metadata, including deterministic CVSS 4.0 & 3.1, CPE, structured summarization optimized for machine filtering & human triage, and more.
All of this coupled with our new dashboard gives teams something they usually do not get from public feeds, namely the ability to encode triage logic once, trust it, and execute it continuously. That is what makes CVE Inbox and its integrations practical.
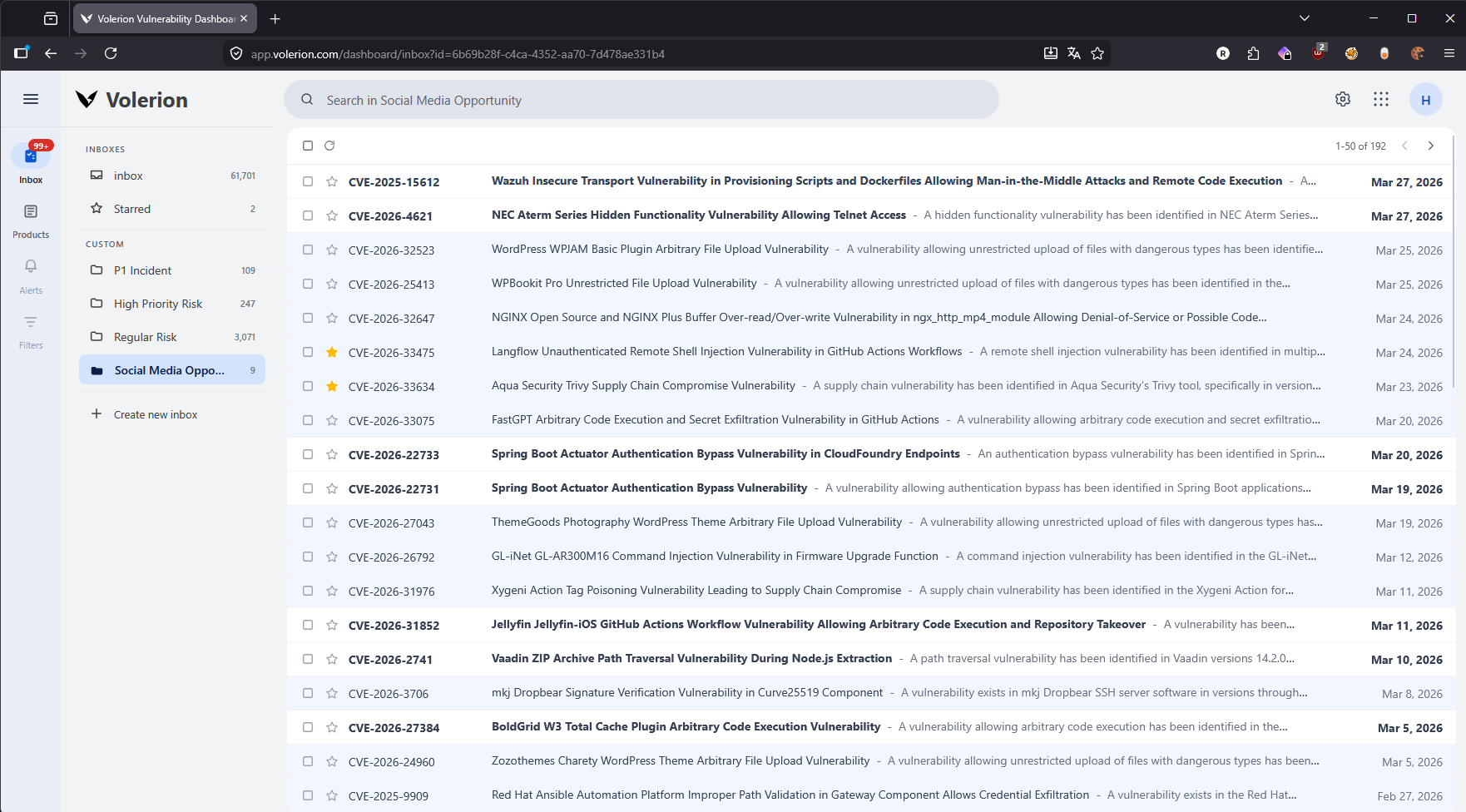
Meet CVE Inbox
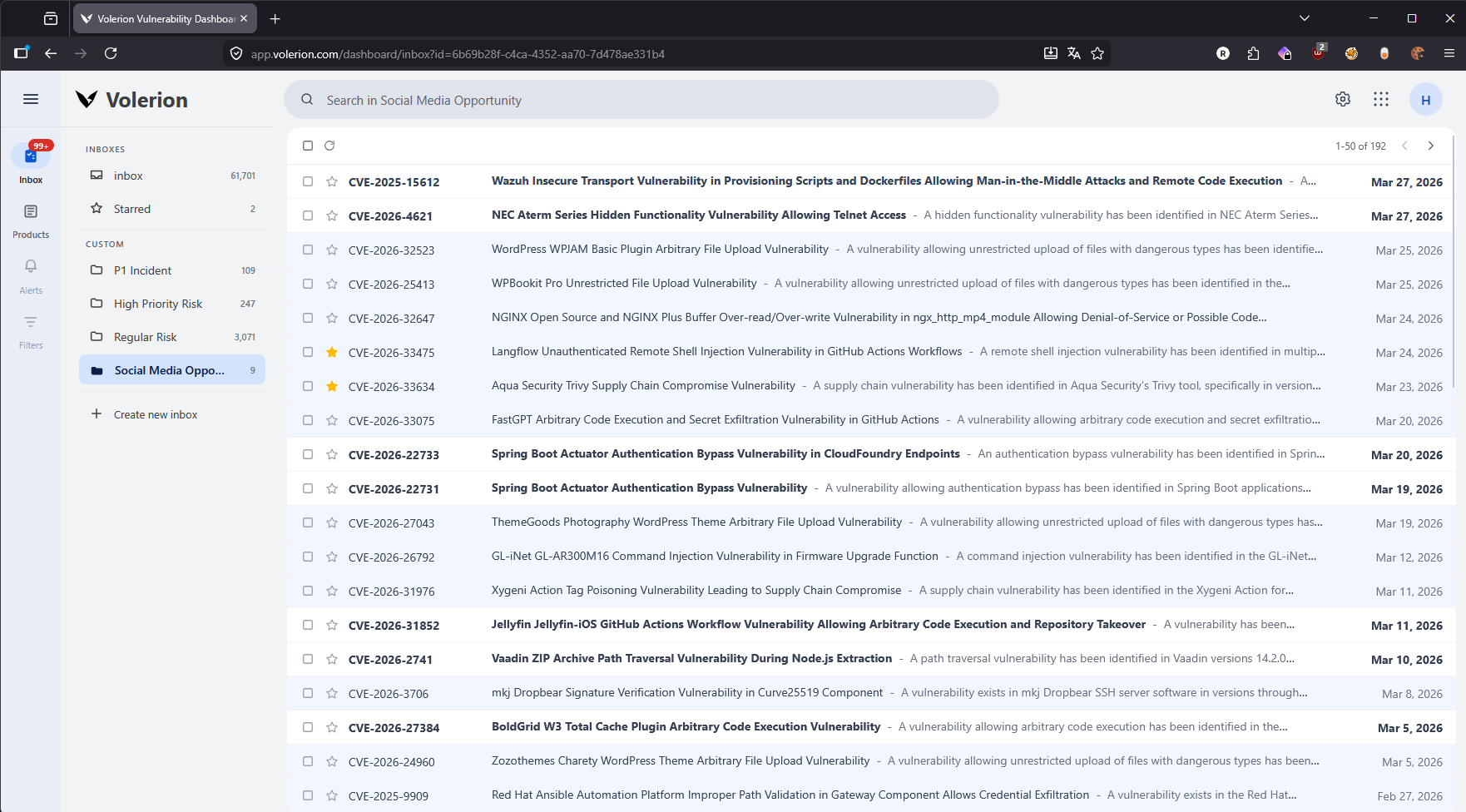
CVE Inbox is the first workflow module built on top of the platform.
Conceptually, it works like email. CVEs arrive continuously, filter policies evaluate each record, and matching records land in specific inboxes.
Operationally, it solves a different problem than a regular search. A search engine asks, “what are you interested in right now?” An inbox asks, “what will you want to see in the future?”
Teams can define dedicated queues for various purposes, including internal incidents, customer outreach, social reporting, technical investigating, and more.
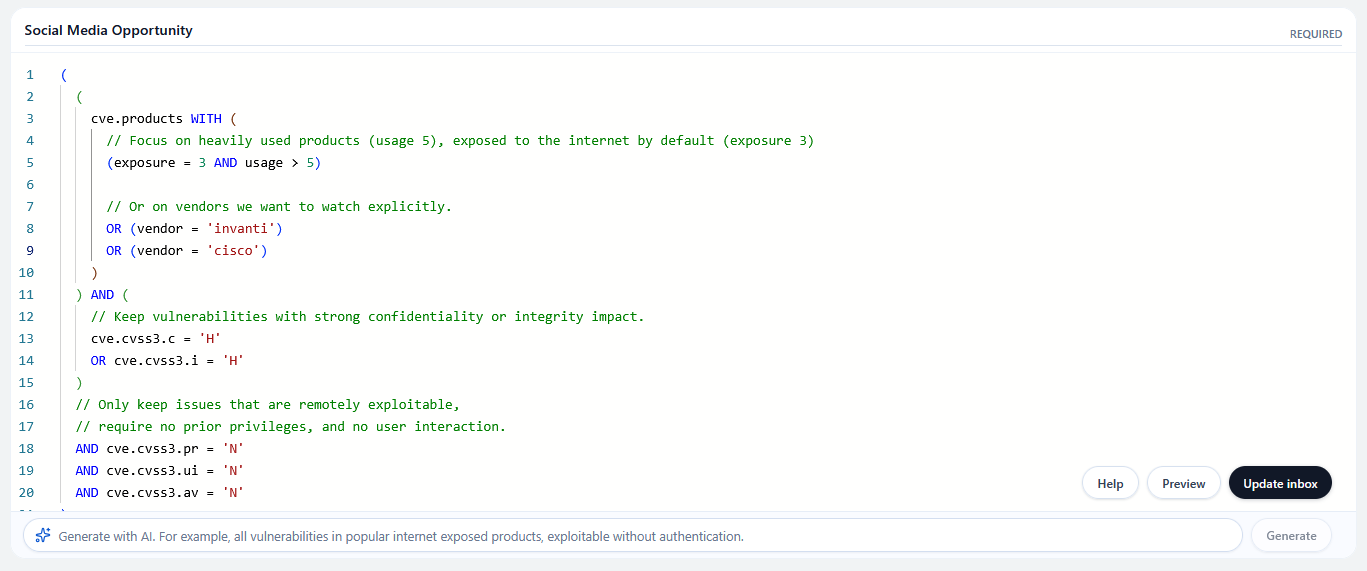
Policy Engine
Most tooling stops at shallow filters built on a few coarse signals, typically scores, flags, or fixed product lists.
That helps to narrow down a list, but it does not let you express a real triage policy. In practice, many dashboards only let teams filter on a final severity score or on a fixed set of products, instead of the metrics that actually matter.
In our platform, filter rules can operate across every relevant aspect of the data model. That means you can filter on product usage and exposure instead of only maintaining a fixed list of products, and filter on attack characteristics such as privileges required, user interaction, and reachability instead of collapsing everything into a single final severity score. The screenshot below shows a real policy query combining exploitability conditions with product exposure and stack relevance.
Practical Use Cases
One of the strengths of the platform is that it is completely customizable. Teams can model inboxes around their own products, their clients’ software stacks, fixed product portfolios, internal escalation criteria, or content workflows.
Some concrete use cases include tracking vulnerabilities for software you or your clients care about, monitoring fixed product sets for exposure changes, detecting P1 incidents as soon as matching CVEs appear, and maintaining dedicated inboxes for social media opportunities, blog post ideas, or deeper technical research.
The point is not to force every team into the same dashboard workflow. The point is to give teams a durable way to encode what matters to them so the right vulnerabilities reliably reach the right people.
Integrations
Inboxes are the core workflow primitive in the platform. That matters because an inbox by itself is only the beginning; integrations are what turn it into an operational system and the easiest way to build on top of our data.
Traditional dashboards usually require teams to keep coming back to the dashboard to see what changed, re-check saved views, and manually push decisions into the rest of their workflow. We think that model breaks down quickly when volume rises.
Once a vulnerability lands in an inbox, teams can route it into the systems where work already happens. That can mean sending issues into a ticketing platform, posting high-priority matches into a messaging app such as Slack, passing a vulnerability into a downstream pipeline of agents, or running post-processing steps tailored to the inbox.
Those post-processing steps can be practical and concrete: automatically proposing social media copy, generating a draft blog post, triggering deeper research on selected vulnerabilities, or enriching the record further before a human ever sees it.
That is why we think about inboxes as the center of the workflow layer. They let teams encode the core decision once, then build on it through integrations and automation without having to check the dashboard every other day to see whether something new needs attention.
Deployment
The platform is available in two operating models, with a hosted service for teams that want rapid onboarding and self-deploy for teams with an active Volerion API key and internal control requirements.
Both models are built on the same data foundation and query capabilities.
For organizations already ingesting NVD-like feeds, integration can be incremental. Start with a narrow inbox policy, validate signal quality, then expand into broader triage automation.
Private Beta
We are currently in private beta (invite-only).
This phase is focused on teams that want to pressure-test real workflows, not toy demos. We are specifically interested in scenarios where current dashboards or alert pipelines are creating noise, missed prioritization, or inconsistent downstream actions.
If that sounds familiar, we would like to work with you.
Want to see whether Volerion fits your workflow? Email contact@volerion.com or schedule a meeting. If you share your current triage use case, we can show you how to turn it into the right inboxes, filters, and downstream integrations.